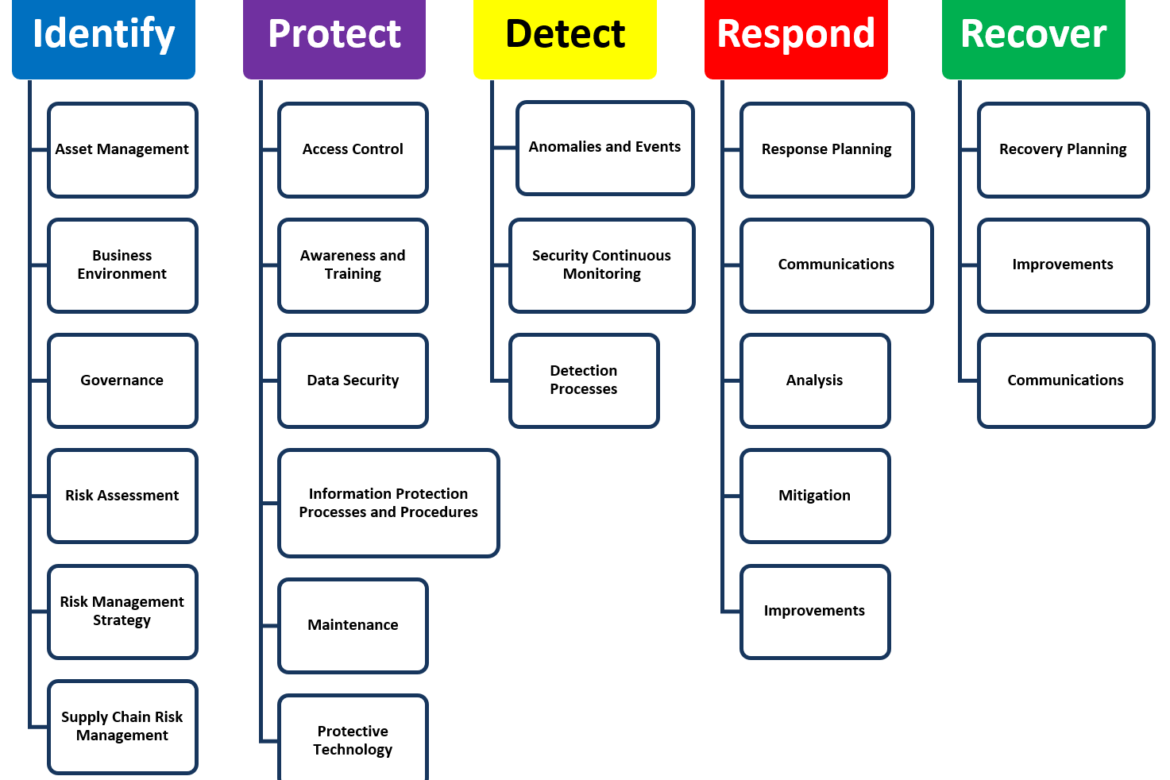
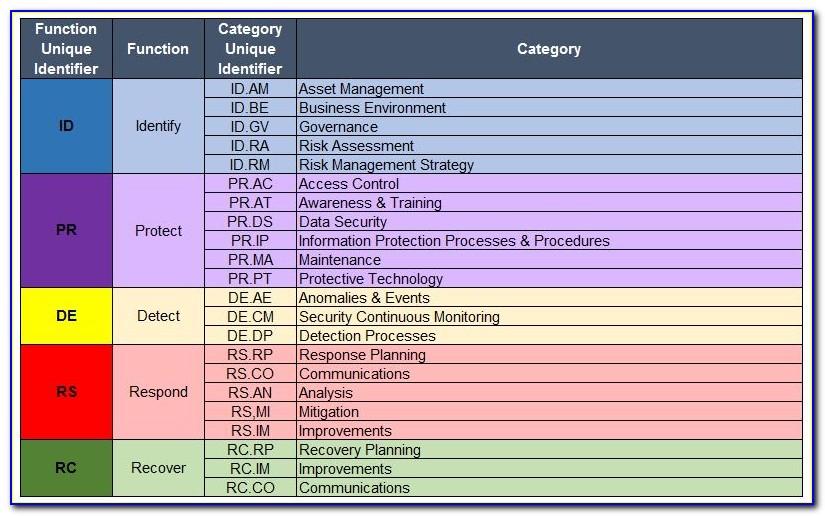
Enchange Management Policy Template Nist - 2019 NCSR Sans Policy Templates 3 NIST Function Identify Identify Asset Management ID AM ID AM 5 Resources e g hardware devices data time and software are prioritized based on
Authority This publication has been developed by NIST to further its statutory responsibilities under the Federal Information Security Modernization Act FISMA of 2014 44 U S C 3551 et seq Public Law P L 113 283
Enchange Management Policy Template Nist
Enchange Management Policy Template Nist
This publication has been developed by NIST to further its statutory responsibilities under the Federal Information Security Modernization Act of 2014, 44 U.S.C. § 3551 et seq., Public Law (P.L.) 113-283. NIST is responsible for developing information security standards and guidelines, including minimum
Cisecuritymsisac Introduction1 NIST Function Identify 2 Identify Asset Management ID AM 2 Identify Supply Chain Risk Management ID SC 3
Span Class Result Type
Cisecurityms isac NIST Function Identify Page 3 ID SC 4 Suppliers and third party partners are routinely assessed using audits test results or other forms of evaluations to confirm they are meeting their contractual
Nist 800 Risk Assessment Template Https Www Mitre Org Sites Default
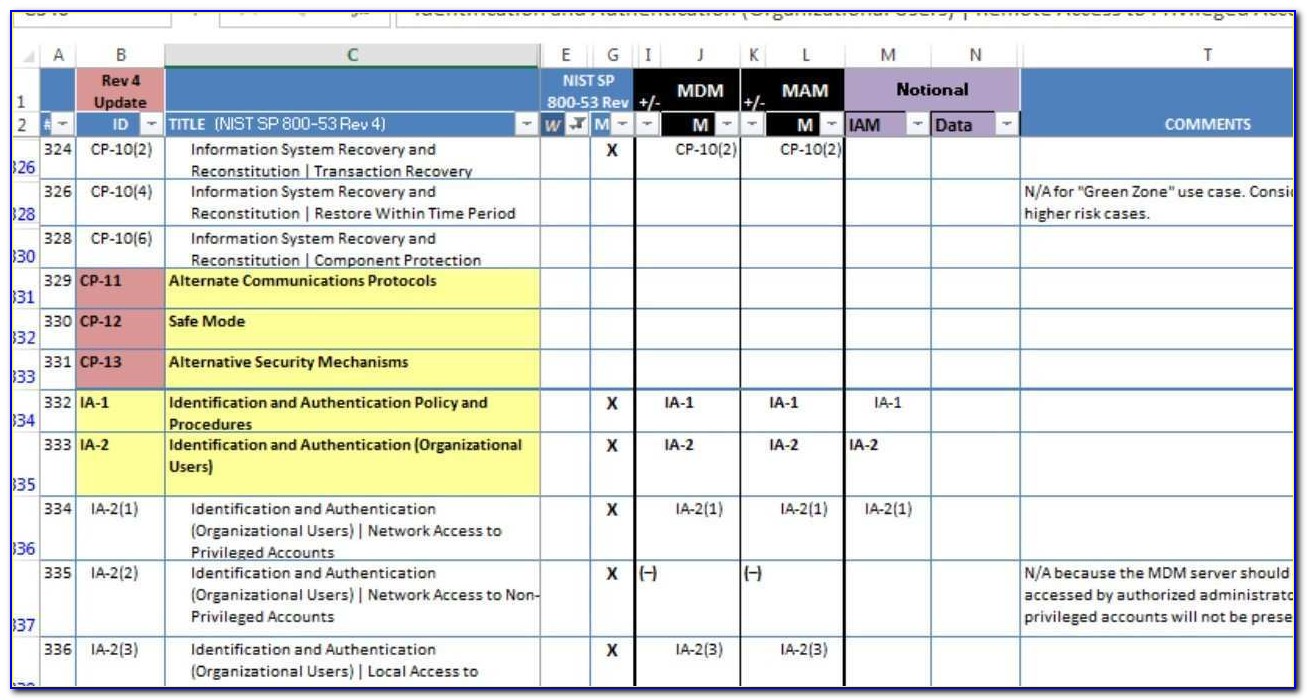
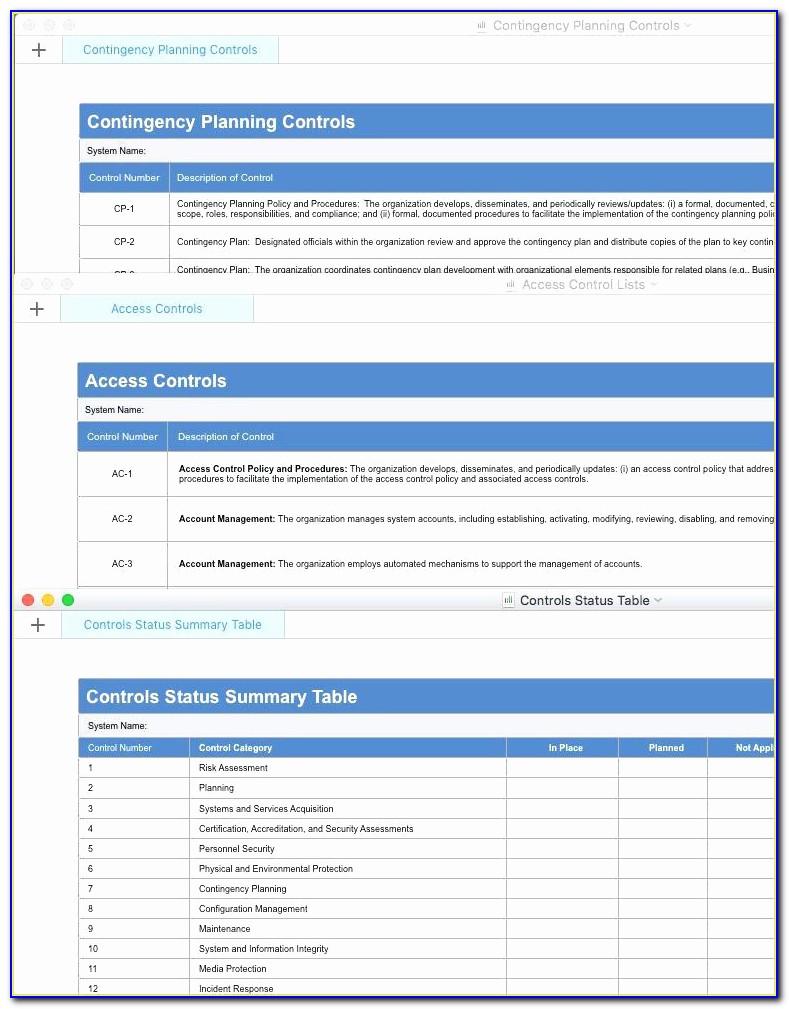
CRR Supplemental Resource Guide Volume 3 Configuration and Change Management Version 1 1
Nist Risk Assessment Template Xls TUTORE ORG Master Of Documents
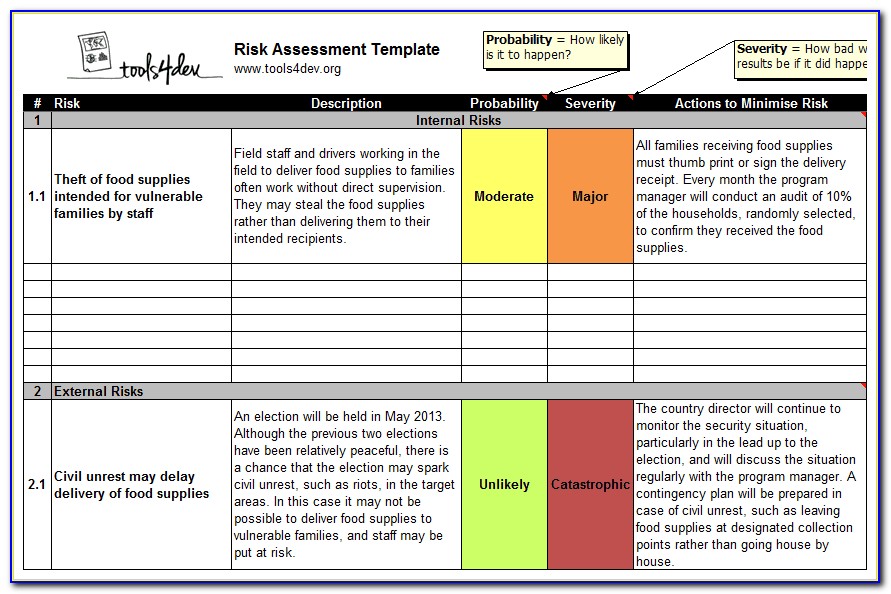
Nist 800 Risk Assessment Template Nist Audit Checklist Auditgaps Riset
Span Class Result Type
This publication has been developed by NIST to further its statutory responsibilities under the Federal Information Security Modernization Act FISMA of 2014 44 U S C 3551 et seq Public Law P L 113 283
Cyber Risk Assessment Template
The purpose of this document is to establish Configuration Management CM concepts to be applied in support of the STEP STandard for the Exchange of Product model data development effort Configuration management is the management of change It is a formal discipline which provides methods and tools a to identify components versions and
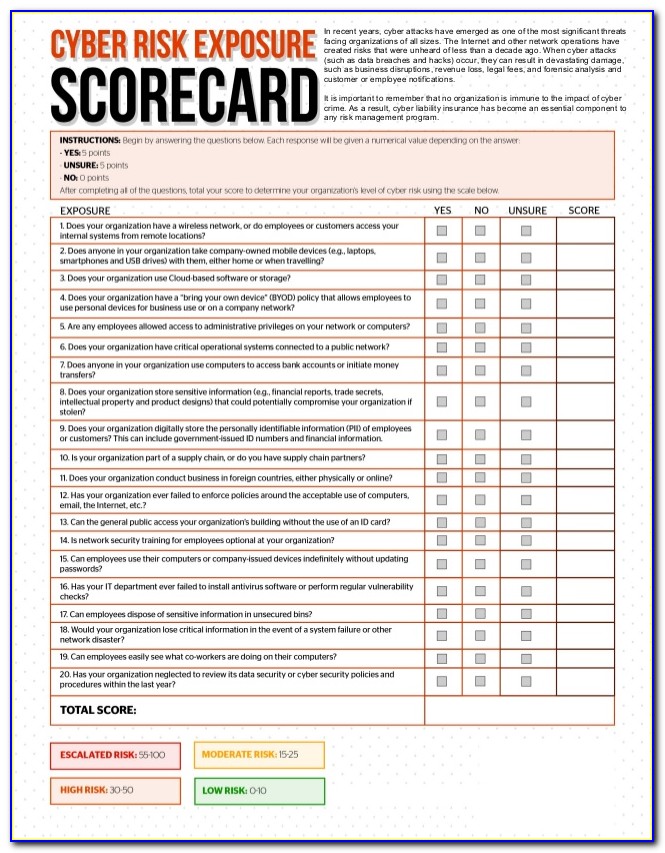
Adequate security of information and information systems is a fundamental management responsibility. Nearly all applications that deal with financial, privacy, safety, or defense include some form of access (authorization) control. Access control is concerned with determining the allowed activities of legitimate users, mediating every attempt by a user to access a resource in the system. In ...
Span Class Result Type
Organizations frequently share information through various information exchange channels based on mission and business needs In order to protect the confidentiality integrity and availability of exchanged information commensurate with risk the information being exchanged requires protection at the same or similar levels as it moves from one organization to another
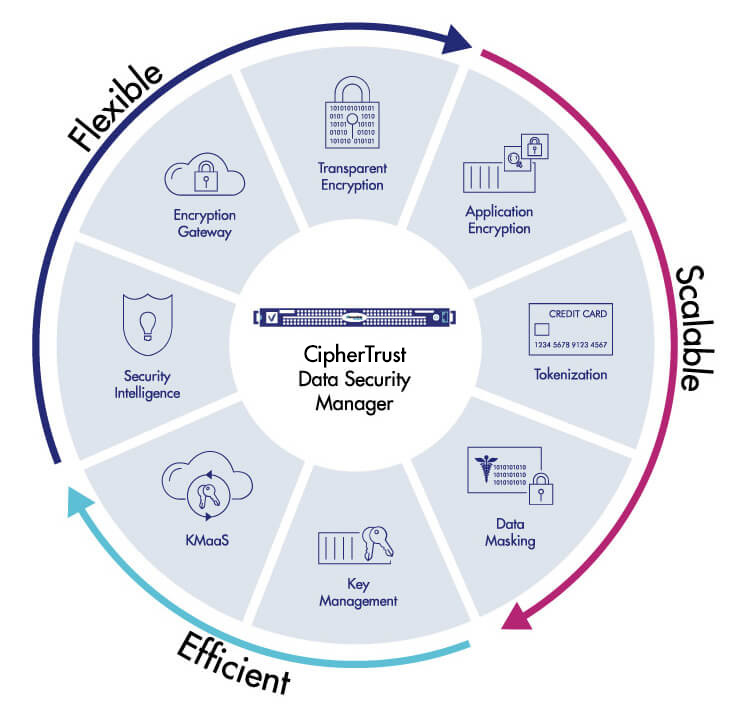
Cryptography Policy Nist
Nist Audit Policy Template
Enchange Management Policy Template Nist
The purpose of this document is to establish Configuration Management CM concepts to be applied in support of the STEP STandard for the Exchange of Product model data development effort Configuration management is the management of change It is a formal discipline which provides methods and tools a to identify components versions and
Authority This publication has been developed by NIST to further its statutory responsibilities under the Federal Information Security Modernization Act FISMA of 2014 44 U S C 3551 et seq Public Law P L 113 283
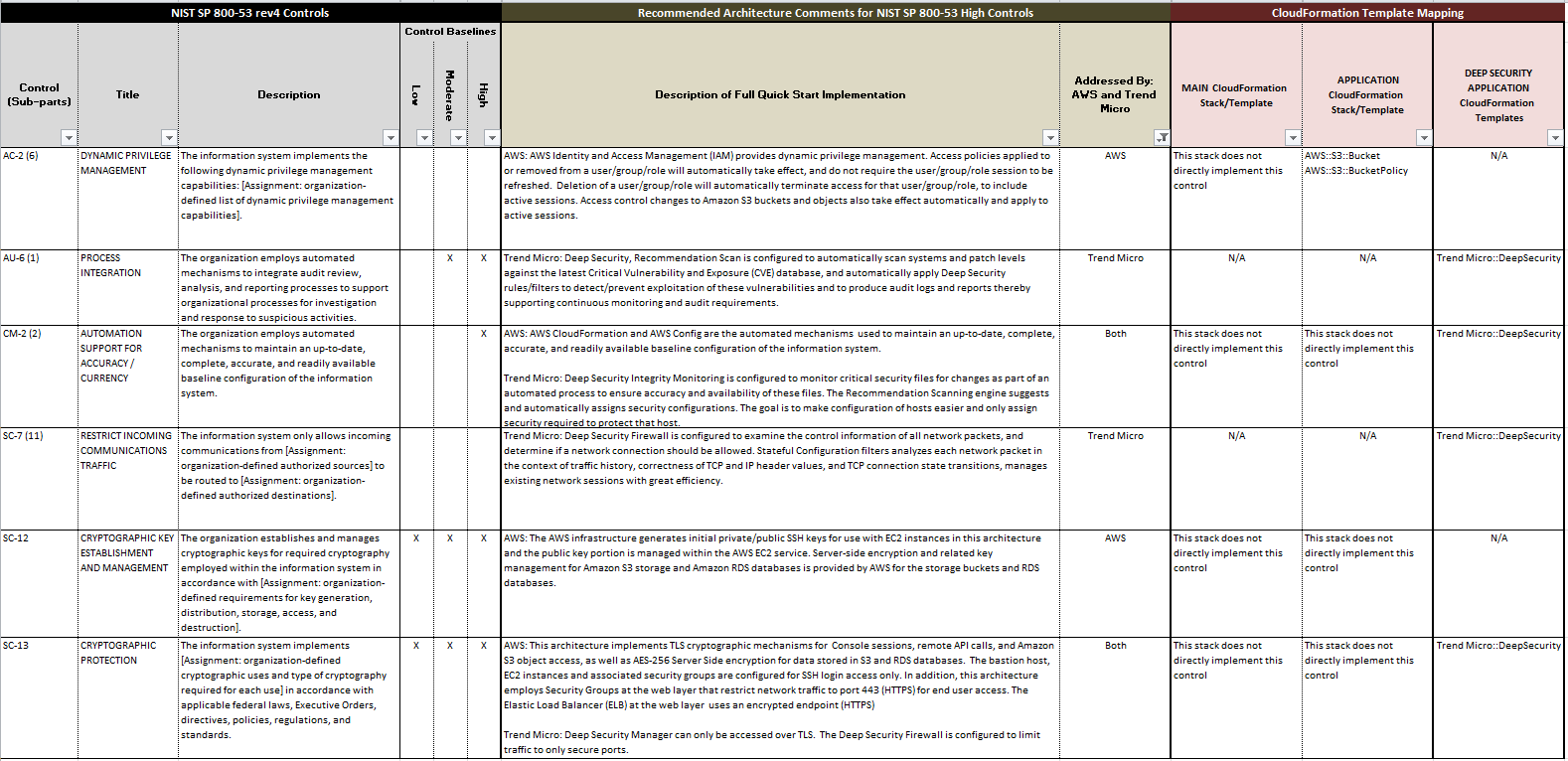
Nist 800 171 Access Control Policy Template
Nist 800 171 Access Control Policy Template Template 1 Resume
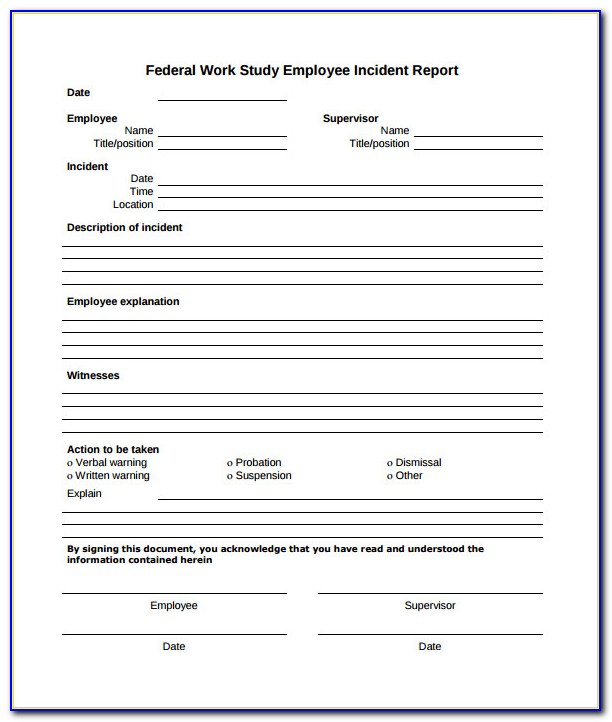
Incident Response Report Template

Nist Information Security Policy Template Merrychristmaswishes info
Nist 800 171 Access Control Policy Template