Encyber Security Risk Register Template - Create a response strategy One of the core elements of your information security risk register is the response strategy Determine how you ll tackle each risk whether by acceptance mitigation transfer or avoidance and document the specific actions required for each scenario 6 Ensure you have risk owners
Here are some of many of the challenges that occur in creating a risk program Crafting a Risk Register Power tool as the base for a multiyear cybersecurity plan Evaluating your controls Linking controls to Best Practice Frameworks Linking the applicable controls to each risk Calculating the controls effectiveness per risk
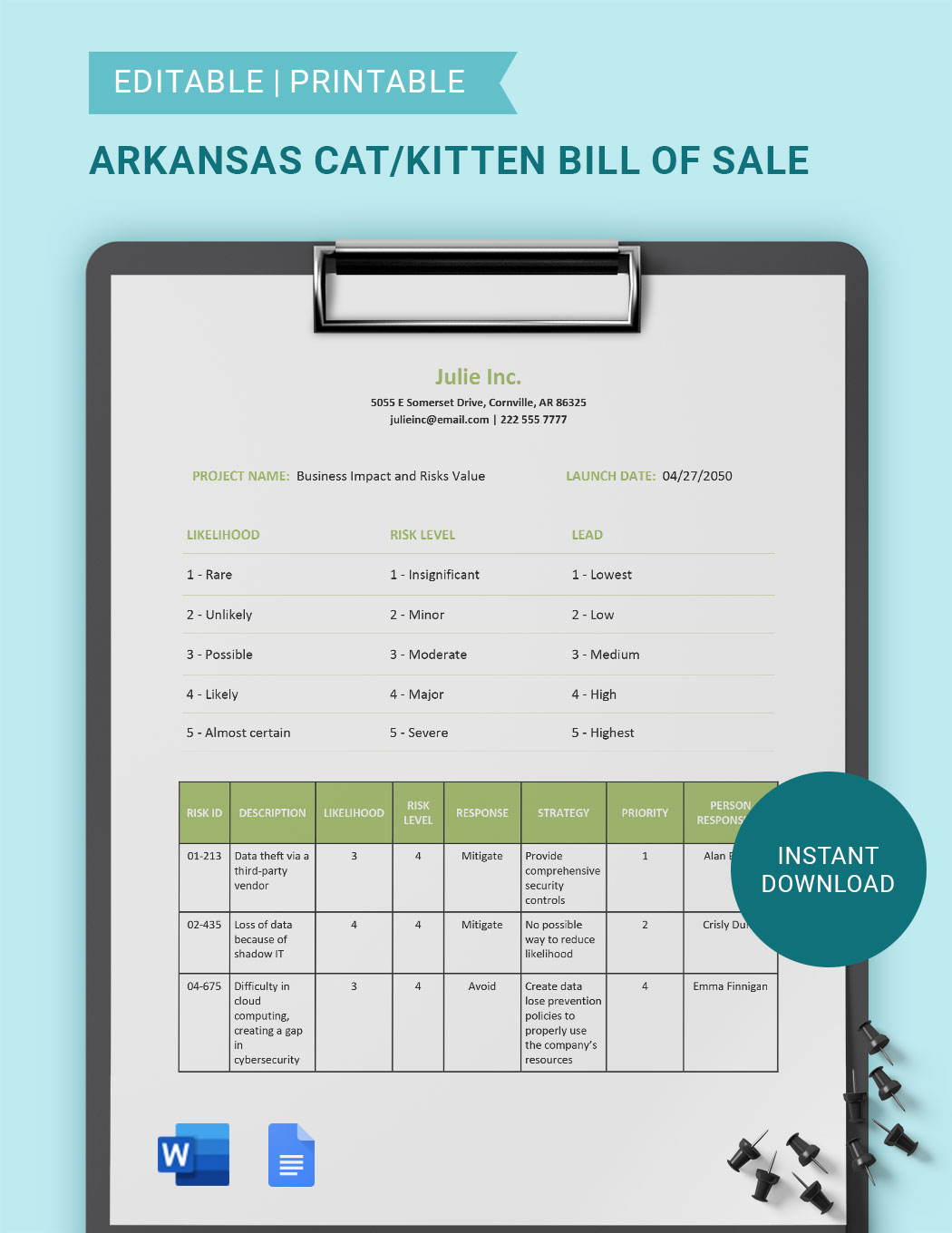
Encyber Security Risk Register Template
Encyber Security Risk Register Template
Many leaders unable visit the full spectrum of online threats against their businesses. How ability risk register help?
Risk registers are a widespread utility among many cybersecurity professionals that allow practitioners to track and measure business risks in one place This type of reporting can quickly help align your teams to the initiatives that matter and save valuable resources time and labor By utilizing compliance scope and efficacy any project
Crafting An Effective Risk Register 2021 03 15 Security Magazine
2 By committing to using a risk register you have to go through a process of gathering all relevant parties and agreeing on a common scale for measuring risks across various business units e g making sure everyone knows when to use a high risk exposure vs a moderate risk exposure
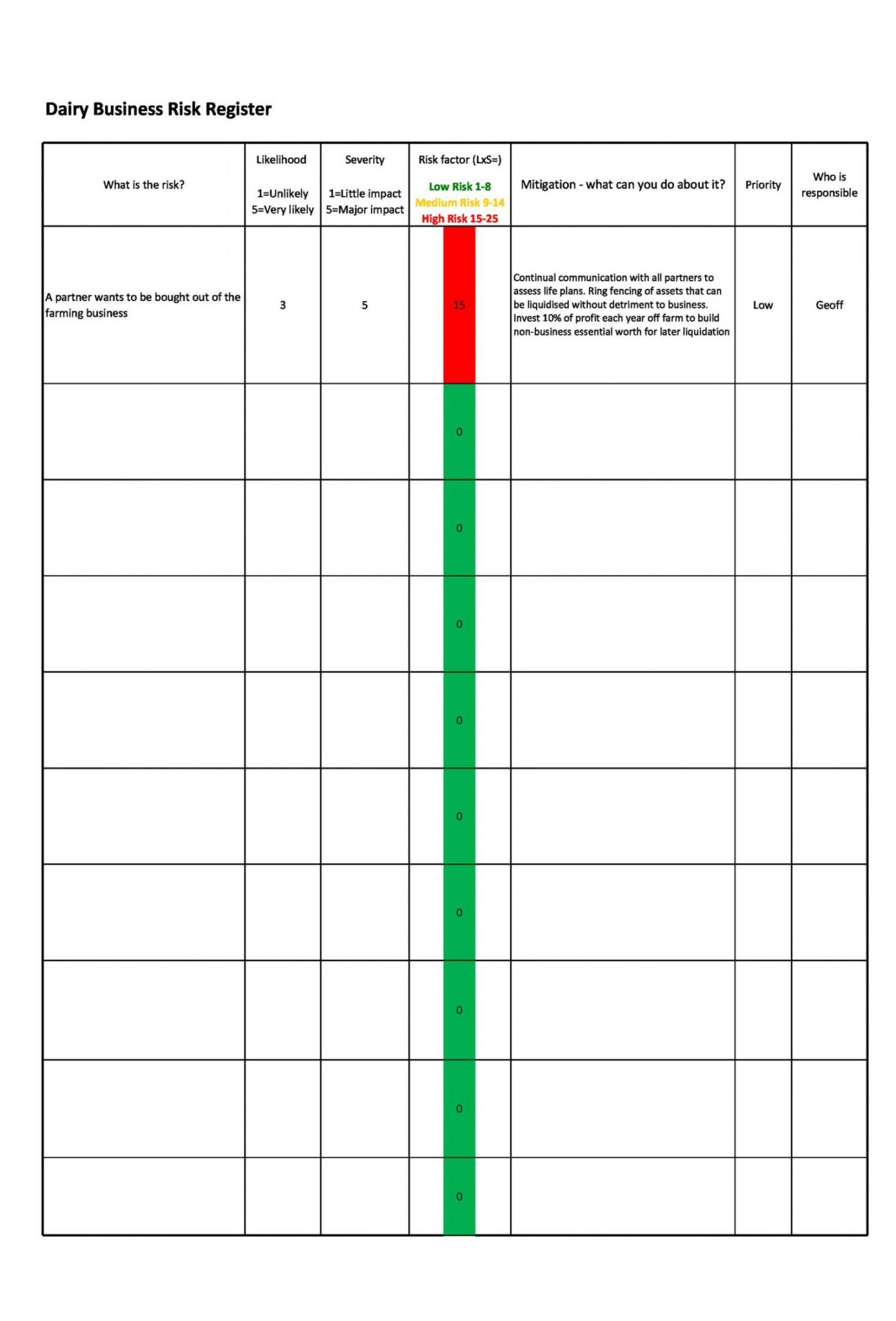
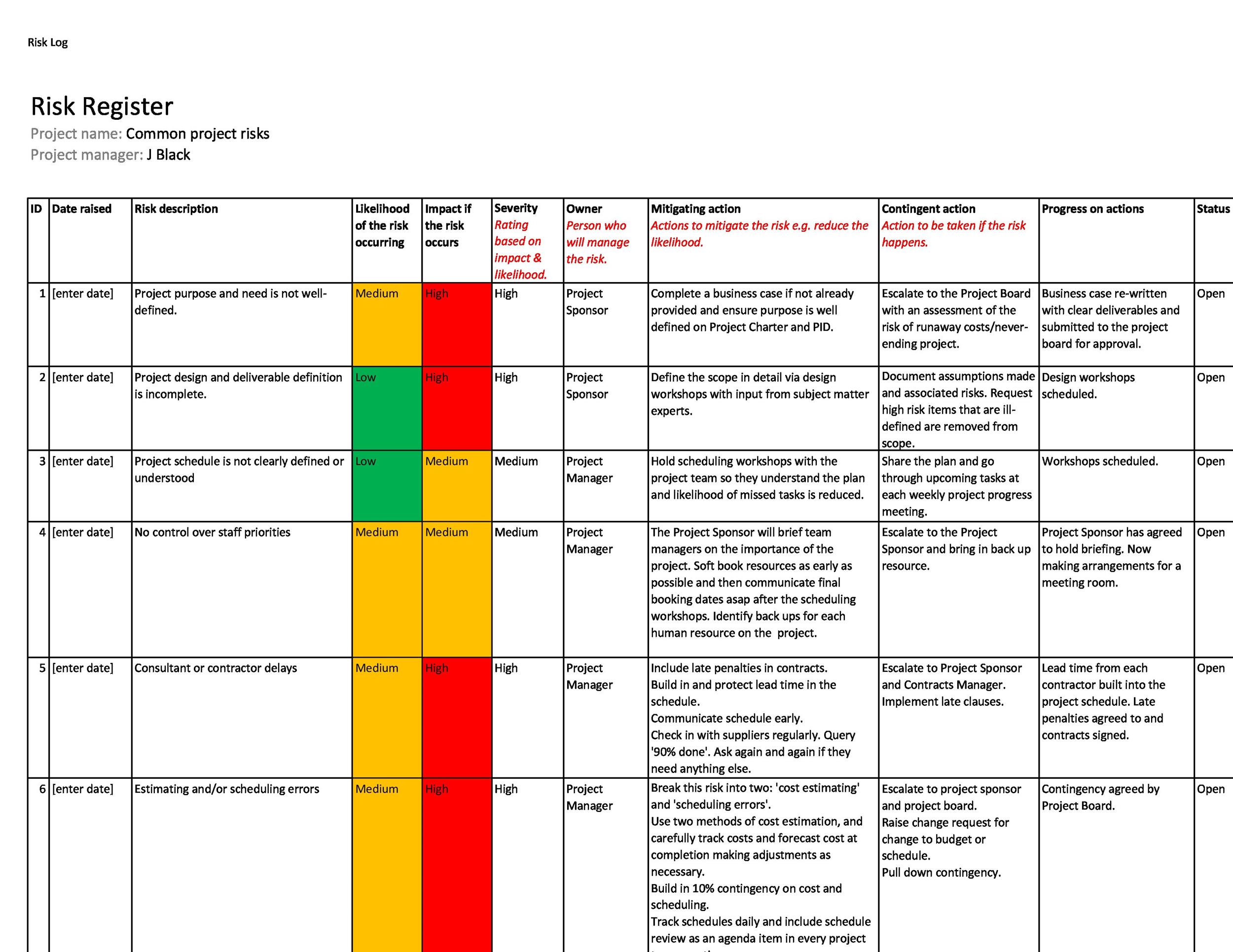
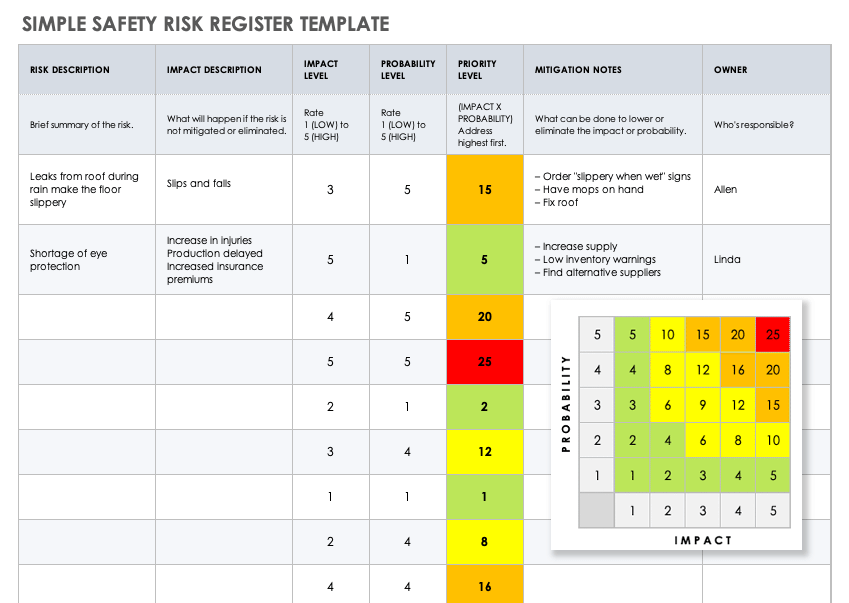
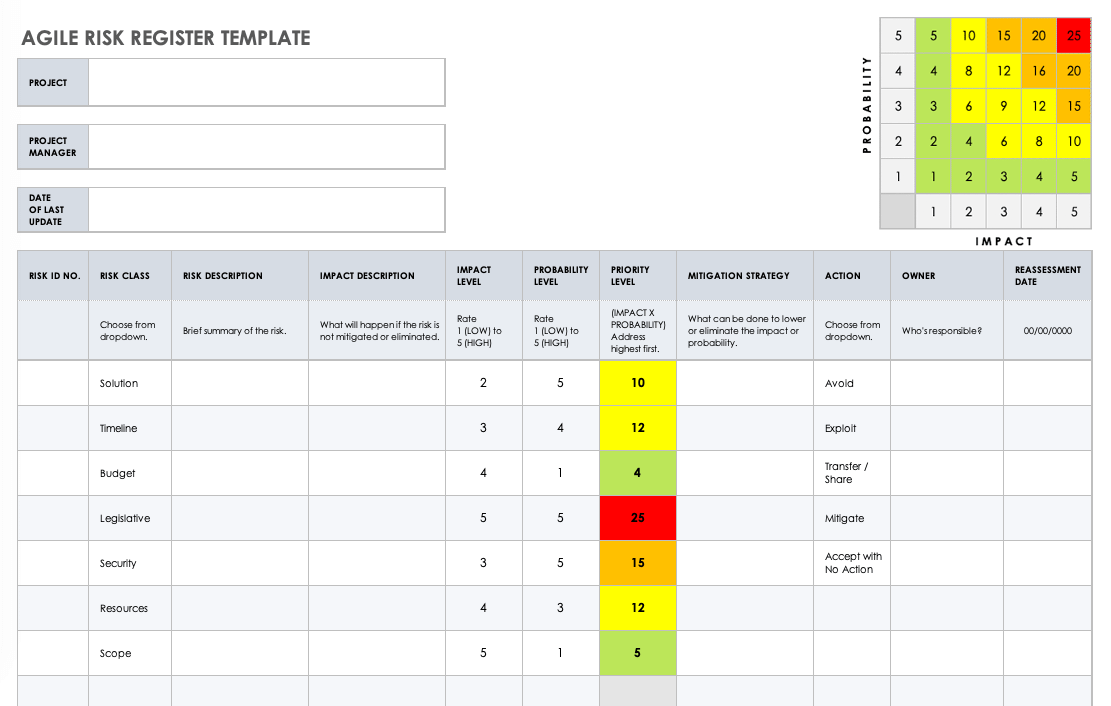
Sample 45 Useful Risk Register Templates Word Excel Templatelab
A cyber risk register template is an essential tool for any organization that wants to effectively manage and mitigate cyber risks Cybersecurity threats are constantly evolving and organizations
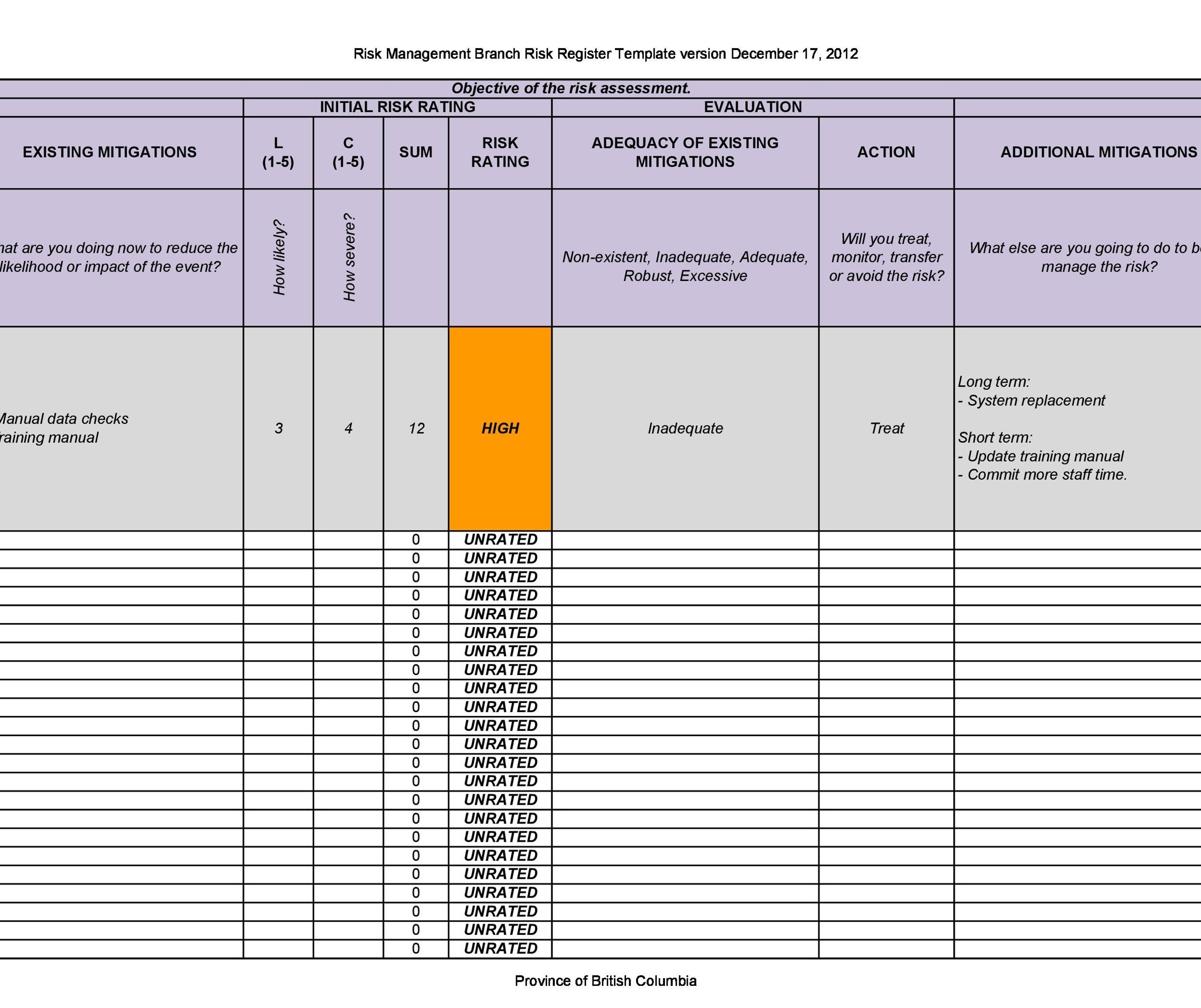
45 Useful Risk Register Templates Word Excel TemplateLab

Cyber Crime Risk Assessment Adam M Erickson
Creating An Information Security Risk Register A StandardFusion
Rezumat Acest document este o traducere n limba rom n a NISTIR 8286A Identifying and Estimating Cybersecurity Risk for Enterprise Risk Management care completeaz NISTIR 8286 Integrating Cybersecurity and Enterprise Risk Management ERM oferind detalii suplimentare privind ghidarea identificarea i analiza riscurilor de securitate cibernetic Acest document face parte dintr o

How To Build A Risk Register Tracker Networks Enteprise Risk And
The risk register template in this cyber security article is meant to provide a sample checklist of risks that your company must take into account during the planning phase Each individual project will vary depending on your company s risk factors and the significance of the project itself The primary purpose of a project risk register is
To answer these questions, and to help security professionals communicate the value of preventative security to their management teams, NIST recently released a document titled "Integrating Cybersecurity and Enterprise Risk Management" (NISTIR 8286). The focal point of this guidance is centered on the usage of a risk register - described as a "repository of risk information" — to ...
Best Guide To Building A Risk Register Examples Template
Evaluate Risks to Labeling Threats both Opportunities For plenty the name risks conjurs upward the idea von terrible events like data injuries serve disruptions ransomware attacks also natural disasters Yet NIST recommends that your take a balanced view when evaluating risks encouraging cybersecurity press risk experts up identify all bezugsquelle of uncertainty both positive
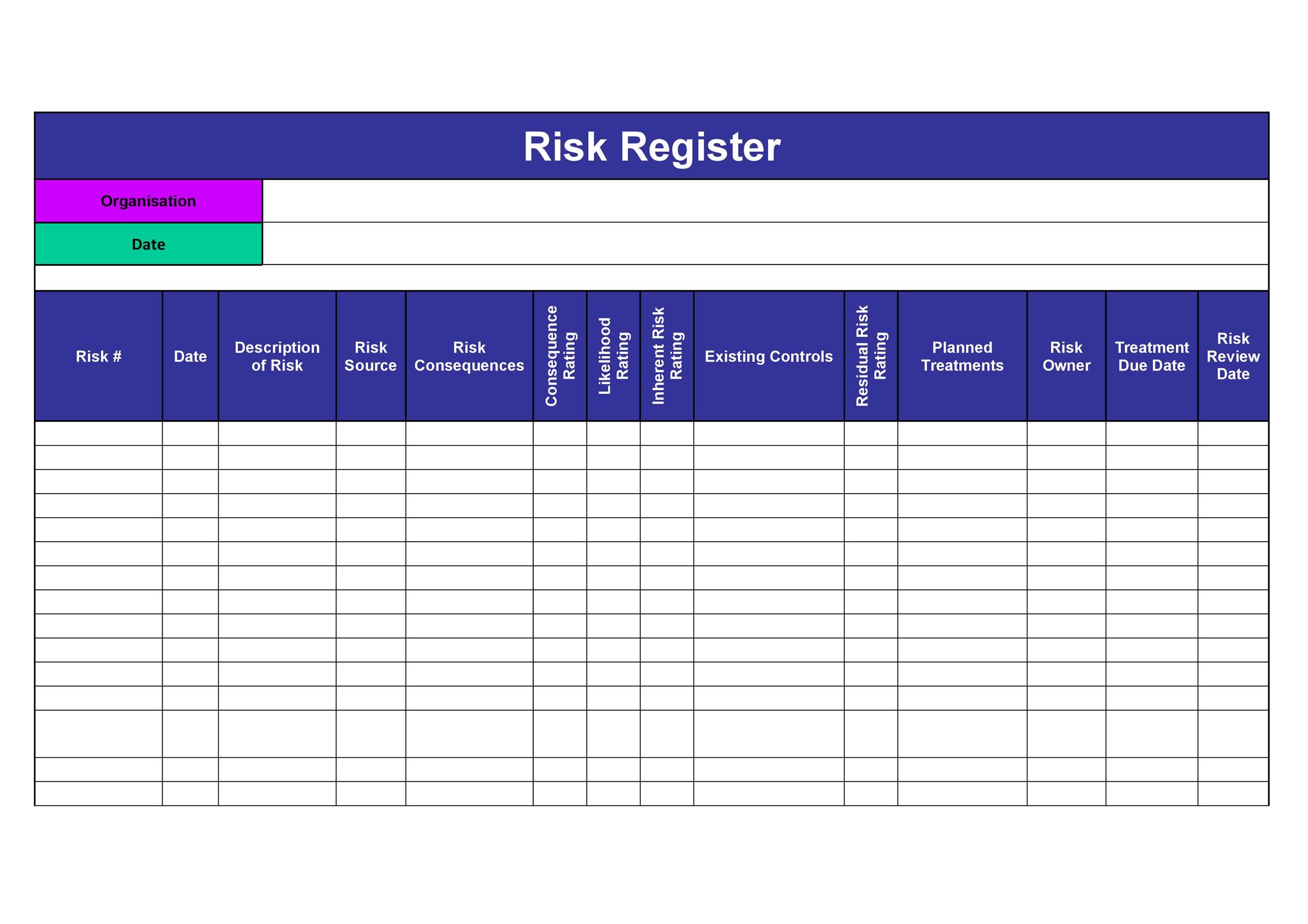
45 Useful Risk Register Templates Word Excel TemplateLab
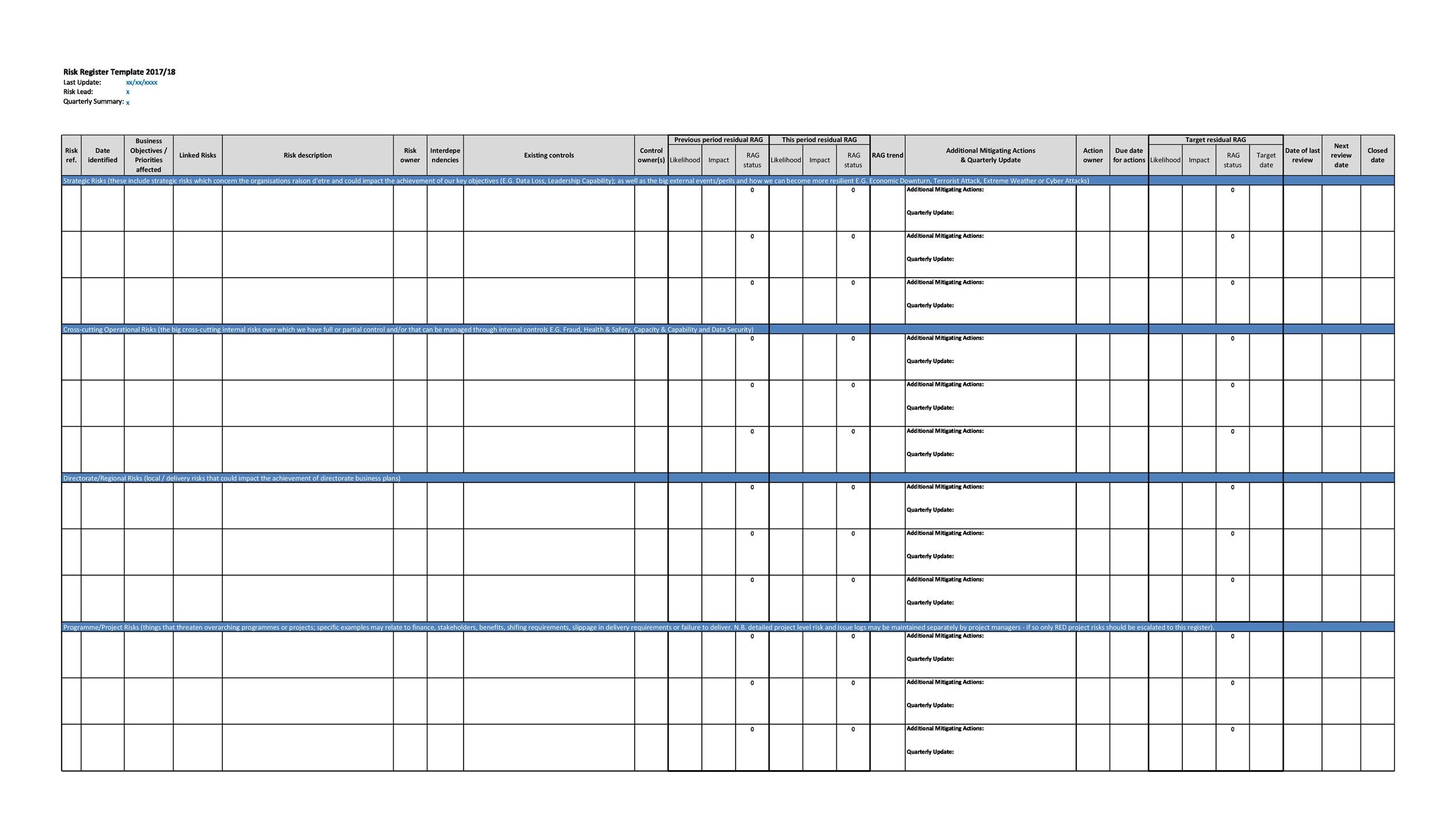
45 Useful Risk Register Templates Word Excel TemplateLab
Encyber Security Risk Register Template
The risk register template in this cyber security article is meant to provide a sample checklist of risks that your company must take into account during the planning phase Each individual project will vary depending on your company s risk factors and the significance of the project itself The primary purpose of a project risk register is
Here are some of many of the challenges that occur in creating a risk program Crafting a Risk Register Power tool as the base for a multiyear cybersecurity plan Evaluating your controls Linking controls to Best Practice Frameworks Linking the applicable controls to each risk Calculating the controls effectiveness per risk
11 Data Center Risk Assessment Template DocTemplates
Managing Risk In A Top Ranked Register 2023 Guide AtOnce
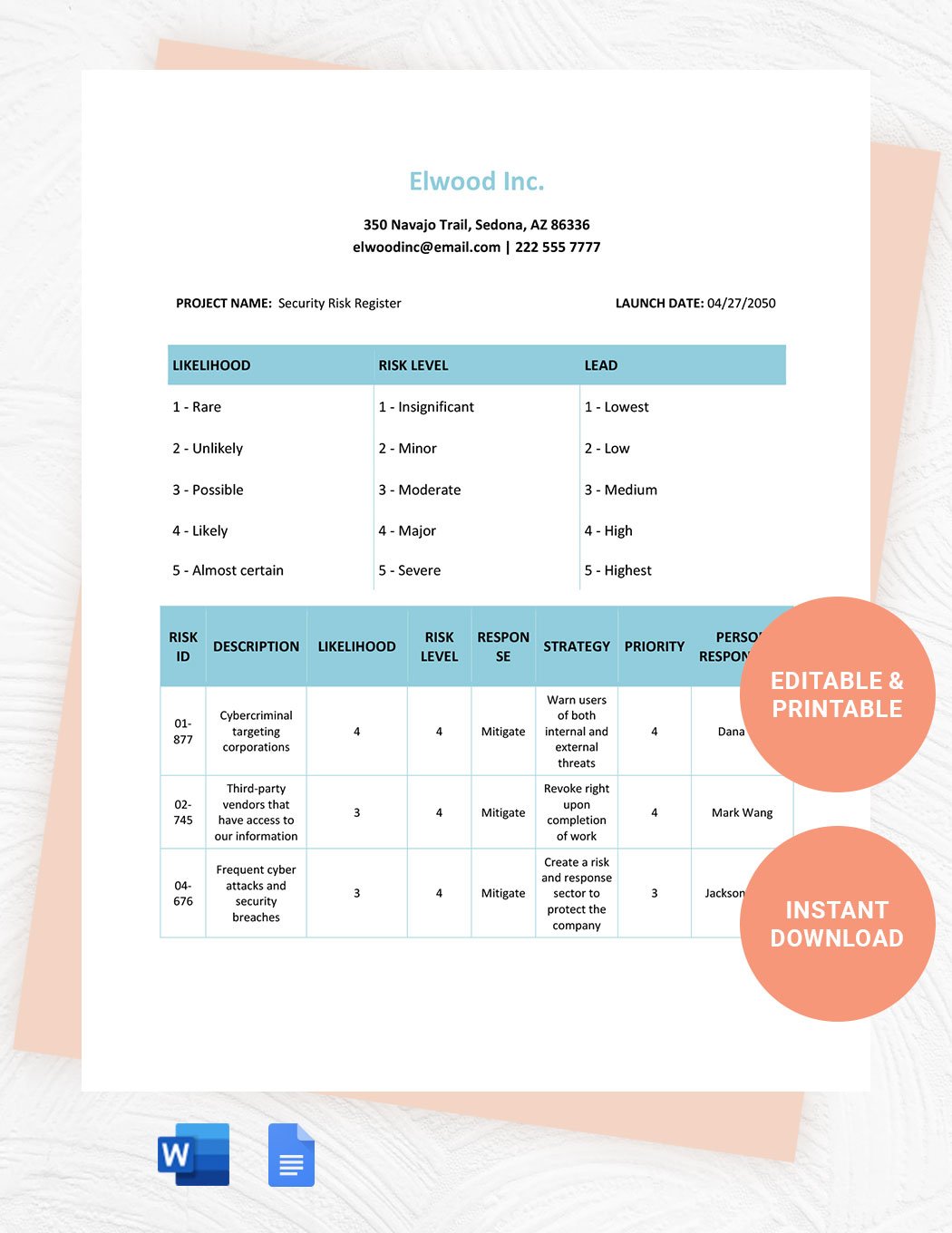
Security Risk Register Download In Word Google Docs Template

Casual Risk Register Excel Estimate Template
Internal Audit Risk Register Template Google Docs Word Template