Eninformation Security Procedures Template - NSC Data and Information Security Procedures Template Ver 1 September 2021 Procedure Identifying Elements Susceptible to Harm Preamble This is a required procedure of a comprehensive Data and Information Security Policy This procedure outlines steps required to determine whether an Element of Conservation Concern warrants the Elements Susceptible to Harm designation due to the risk that
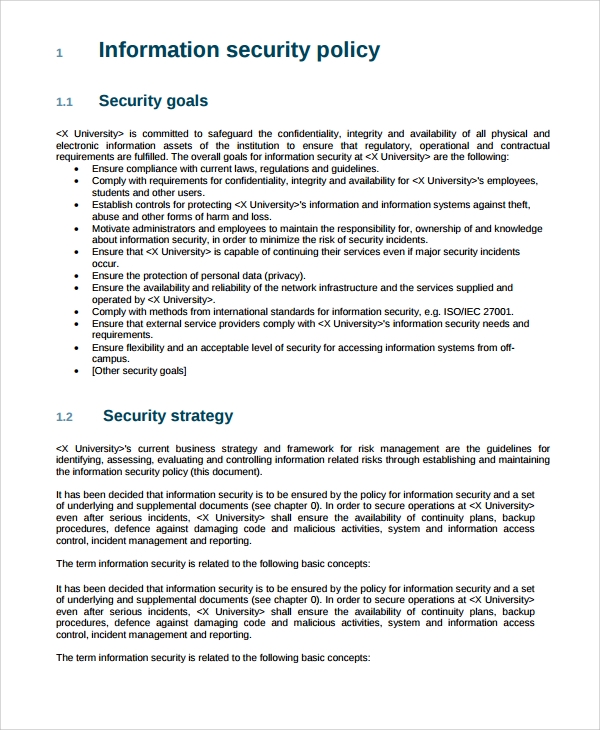
10 5 Minute Read An information security policy is a set of rules guidelines and procedures that outline how an organization should manage protect and distribute its information assets The policy aims to reduce the risk of data breaches unauthorized access and other security threats by providing a structured approach to information security management
Eninformation Security Procedures Template
Eninformation Security Procedures Template
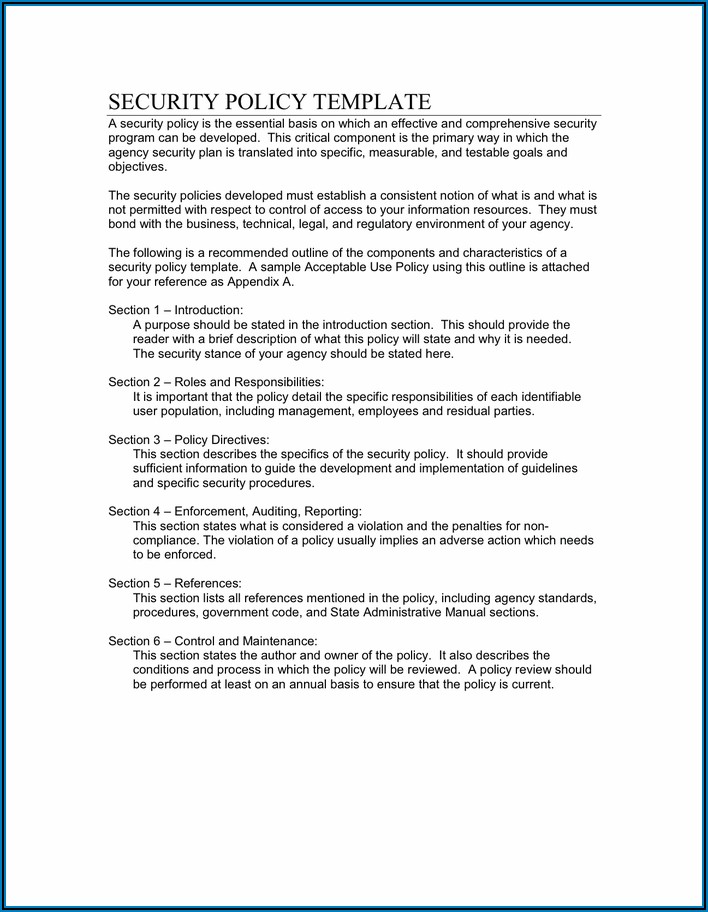
An information security policy can be tough to build from scratch; it needs to be robust and secure your organization from all ends. It should cover all software, hardware, physical parameters, human resources, information, and access control. It also needs to be flexible and have room for revision and updating, and, most importantly, it needs ...
Cisecurityms isac NIST Function Protect Page 4 NIST FUNCTION Protect Protect Identity Management and Access Control PR AC PR AC 1 Identities and credentials are issued managed verified revoked and audited for
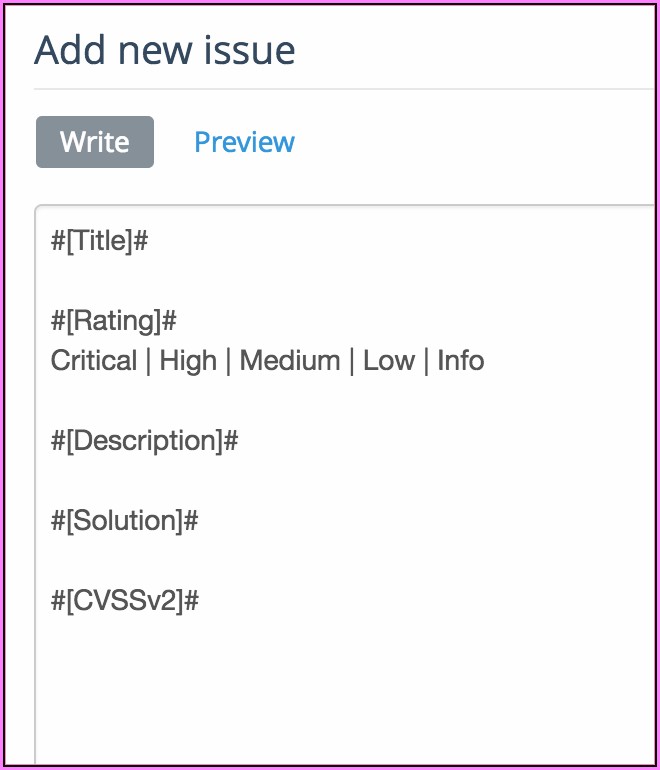
Information Security Policy Examples 11 Key Elements HackerOne
Adapt existing security policies to maintain policy structure and format and incorporate relevant components to address information security Establish a project plan to develop and approve the policy Create a team to develop the policy Schedule management briefings during the writing cycle to ensure relevant issues are addressed
Cyber Security Risk Assessment Report Template Template 1 Resume
2 2019 NCSR Sans Policy Templates Introduction The Multi State Information Sharing Analysis Center MS ISAC is offering this guide to the SLTT community as a resource to assist with the application and advancement of

C Tpat Security Procedures Manual By PatrickShephard3001 Issuu
C TPAT Security Policies And Procedures Computer Security Security
Span Class Result Type
7 219 NCSR SANS Policy Templates Respond Improvements RS IM RS IM 1 Response plans incorporate lessons learned SANS Policy Template Data Breach Resp onse Policy SANS Policy Template Pandemic Response Plan ning Policy SANS Policy Template Security Response Plan Policy RS IM 2 Response strategies are updated
Sample Information Security Policy Template Locedos
Standards and safeguards are used to achieve policy objectives through the definition of mandatory controls and requirements Procedures are used to ensure consistent application of security policies and standards Guidelines provide guidance on security policies and standards Tools and forms related to these are also maintained here
It is a tool that alerts the organization on the security risks they face and guides them on how they should counter them and to what degree. It also informs people as to what actions are ...
Build Strong Information Security Policy Template Examples
In this article we lay bare the ISO 27001 information security policy Exposing the insider trade secrets giving you the templates that will save you hours of your life and showing you exactly what you need to do to satisfy it for ISO 27001 certification We show you exactly what changed in the ISO 27001 2022 update
Trucking Policy And Procedures Template Template 2 Resume Examples
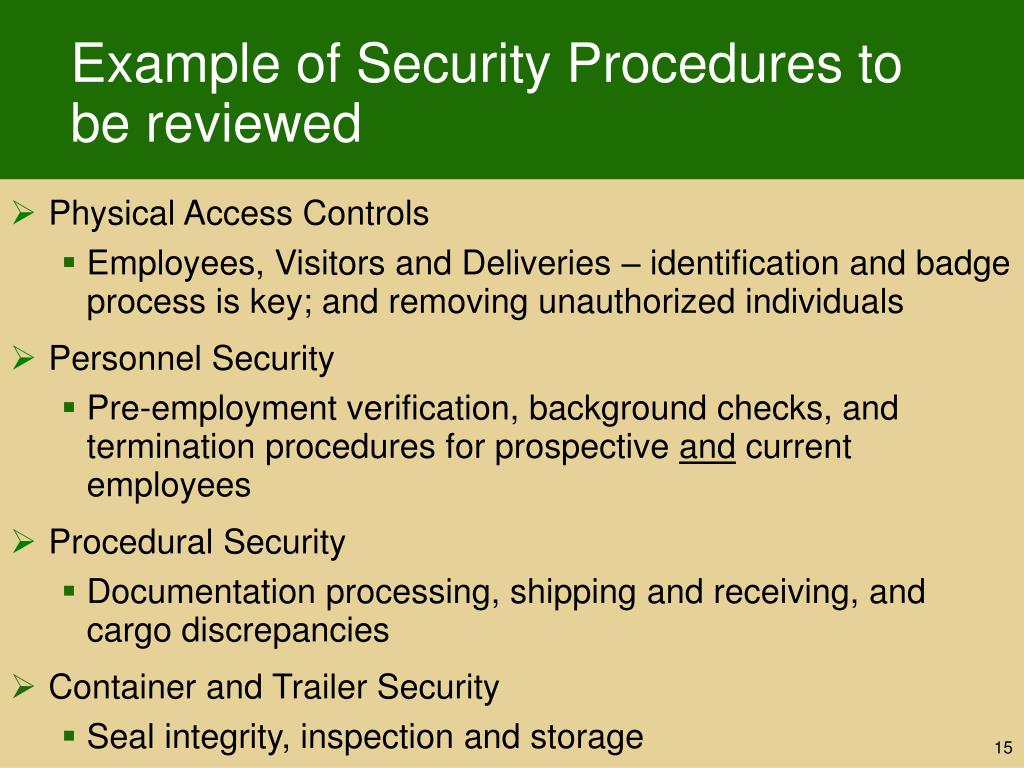
PPT National Conference On SAFE TRADE AEO CTPAT Six Years On A
Eninformation Security Procedures Template
Standards and safeguards are used to achieve policy objectives through the definition of mandatory controls and requirements Procedures are used to ensure consistent application of security policies and standards Guidelines provide guidance on security policies and standards Tools and forms related to these are also maintained here
10 5 Minute Read An information security policy is a set of rules guidelines and procedures that outline how an organization should manage protect and distribute its information assets The policy aims to reduce the risk of data breaches unauthorized access and other security threats by providing a structured approach to information security management
Information Security Policy Framework Template PDF Template
Security Policy Template Free Database

CTPAT Agricultural Security Requirements Top 8 FAQ Veroot
Information Security Policies Procedures And Standards Template

Information Security Policies And Procedures Template Template 1
