Envulnerability Management Template - Check out our free Google Doc template for building a risk based vulnerability management policy including A detailed methodology for calculating the risk posed by software vulnerabilities Clearly defined roles and responsibilities for business and security leaders Easily modifiable entries that allow for customization based on your
Policy Endpoint Protection Anti Virus Malware All Company owned and or managed Information Resources must use the Company IT management approved endpoint protection software and configuration All non Company owned workstations and laptops must use Company IT management approved endpoint protection software and configuration prior to any connection to a Company Information
Envulnerability Management Template

Envulnerability Management Template
A robust vulnerability management program can help organizations: Prioritize vulnerabilities based on risk and exposure. Prevent the introduction of known vulnerabilities. Maintain compliance with security standards and regulations. Minimize the overall attack surface. Understand and improve their security posture.
This Vulnerability Management Policy Outlines the expectations requirements basic procedures for Vulnerability Identification Vulnerability Evaluation Vulnerability Mitigation Vulnerability
Vulnerability Management Policy Template FRSecure
Overview Develop a plan to continuously assess and track vulnerabilities on all enterprise assets within the enterprise s infrastructure in order to remediate and minimize the window of opportunity for attackers Monitor public and private industry sources for new threat and vulnerability information
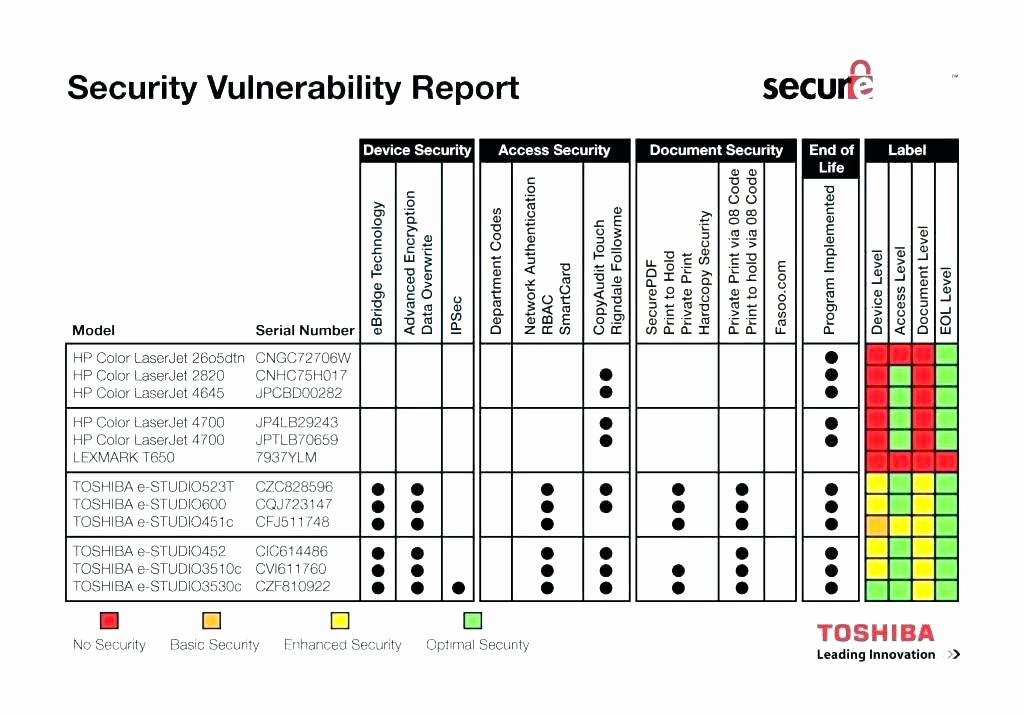
Vulnerability Management Program Template Stcharleschill Template
As both an example and a starting point eSecurity Planet has developed a free vulnerability management policy template for organizations to download modify to meet their needs and use Notes of
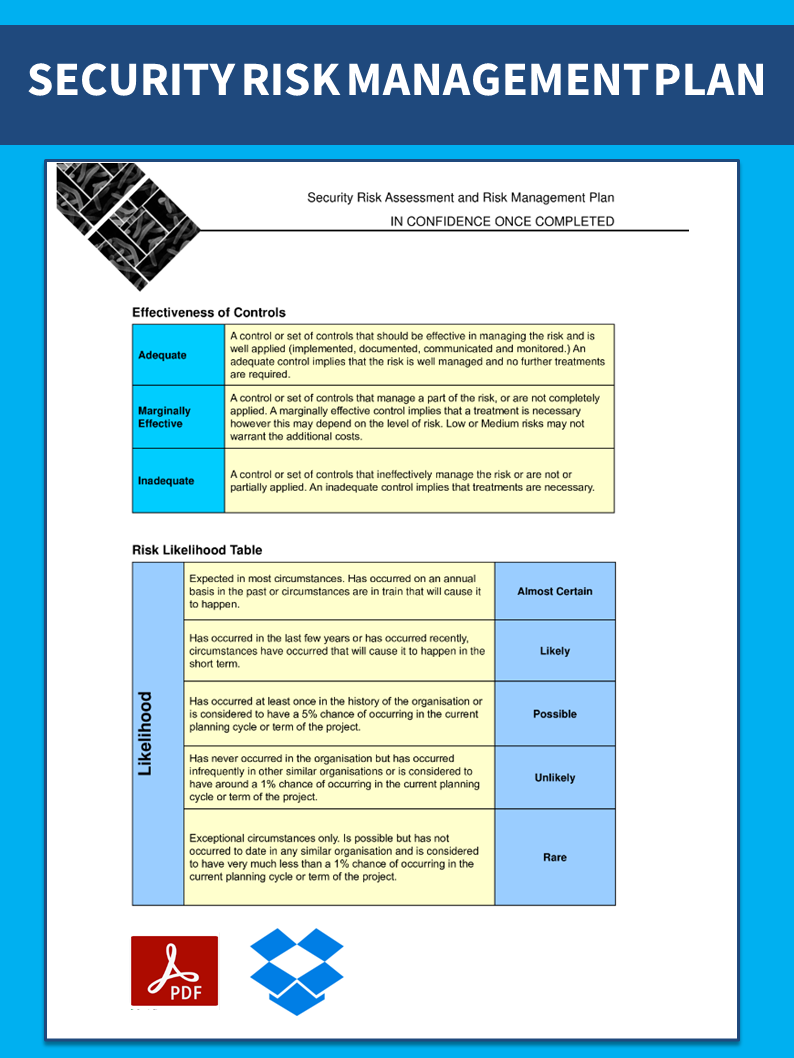
Sample Example Format Templates 11 Sample Risk Management Plan

Fresh Operational Risk Management Template Business Risk Business
Vulnerability Management Policy Template
Understanding and managing vulnerabilities is a continuous activity requiring focus of time attention and resources This policy template is meant to supplement the CIS Controls v8 The policy statements included within this document can be used by all CIS Implementation Groups IGs but are specifically geared towards Safeguards in

Awesome Management Position Resume Template Resume Design Template Cv
Vulnerability Management Plan Template only takes 20 seconds This Vulnerability Management Plan Template provides a structure and guidance to help create a comprehensive plan that identifies and mitigates security risks threats and other potential issues Easily track and manage objectives with Cascade s automated reporting and analytics
In this article, you'll find the most comprehensive selection of free vulnerability assessments, available in Microsoft Excel and Word, PDF, and Google Sheets formats. Each template is fully customizable, so you can tailor your assessment to your business needs. Included on this page are a variety of templates, like Risk Management Matrix ...
A Step By Step Guide To The Vulnerability Management Process Policy
Use this template to Define your approach for vulnerability management to reduce system risks and integrate with patch management Outline the process for identifying scoring and mitigating vulnerabilities Explain how the vulnerability management policy will be enforced Use this vulnerability management policy template to define your

Plan Your Resources And Bridge The Gap Between The Capacity And Demand

Wound Management Template Promotional Video For Your Business YouTube
Envulnerability Management Template
Vulnerability Management Plan Template only takes 20 seconds This Vulnerability Management Plan Template provides a structure and guidance to help create a comprehensive plan that identifies and mitigates security risks threats and other potential issues Easily track and manage objectives with Cascade s automated reporting and analytics
Policy Endpoint Protection Anti Virus Malware All Company owned and or managed Information Resources must use the Company IT management approved endpoint protection software and configuration All non Company owned workstations and laptops must use Company IT management approved endpoint protection software and configuration prior to any connection to a Company Information
Document And Template Management Software
Issue Management Template Momentum Suite

KPI Dashboard Template V2 Tr n B 20 Slides M u V B o C o KPIs Digi 4U

Standard For Quality Control Landing Page Template Stock Vector
Customer Management Spreadsheet Template